
Chief Information Security Officer (CISO): What does this job entail?
Cybersecurity has become a critical issue. If not handled with utmost professionalism, a company can become vulnerable to hackers, leading to dire consequences for its
🚀 Think you’ve got what it takes for a career in Data? Find out in just one minute!

Cybersecurity has become a critical issue. If not handled with utmost professionalism, a company can become vulnerable to hackers, leading to dire consequences for its

CSRF (Cross-site request forgery) or cross-site request forgery is a type of cyberattack. It involves exploiting a user’s active session to send malicious requests without

The ISO 27001 Lead Implementer is an expert in information security, responsible for overseeing the development and deployment of an ISMS that meets the ISO
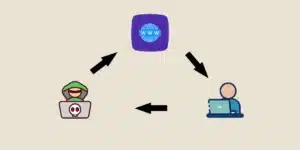
An XSS (Cross-Site Scripting) cyberattack is accessible to all cybercriminals, yet it can have a catastrophic impact on the victims. To understand its potential effects

Protecting data and computer systems has become a top priority for businesses. Conducting a security audit is a fundamental step in assessing and enhancing the

DNS attacks have the potential to disrupt the entire network of a company, crippling its operations for several days and causing substantial losses: downtime for

Discover everything you need to know about vulnerability scanning: definition, benefits, methodology, and tools. A cornerstone of cybersecurity for effectively securing an IT system. What

“Better safe than sorry”… This is the core philosophy behind fuzzing, a method that involves testing software or systems from as many diverse and unforeseeable

Explore the Role of a Pentester: This cybersecurity professional protects data by identifying system vulnerabilities through controlled attacks. Their expertise defends businesses against security breaches.

The Punycode attack is an alarmingly effective phishing technique that exploits a web technology. Learn about its mechanisms, its implications, and the various ways to

SSL, or Secure Sockets Layer, is one of the initial technologies developed to secure online exchanges by establishing an encrypted connection between a user and

Enough is enough… Cyberattacks have inflicted significant damage on European organizations. The impact was profound not only on these companies but also on many essential

