More sophisticated, more aggressive, and better equipped, modern cyber attacks are formidable. To counter them, companies would do well to adopt the same strategies as malicious hackers. This is where pentesting plays a crucial role: an extremely effective method for identifying and exploiting IT vulnerabilities, then addressing them. Discover pentesting, its various forms, methodologies, and more.
What is a pentest?
Pentest definition
A pentest is a penetration test. The pentester penetrates an organization’s computer system (whether through the computer network, a website, an application, an IoT device, …) to identify attack vectors that could jeopardize the confidentiality, integrity, and availability of data. After pinpointing these security weaknesses, the pentester implements the necessary fixes to patch the vulnerabilities or lessen the impact of their exploitation. And this, before a computer hacker discovers them.
It’s kind of like a “preventive cyber attack” or an “offensive evaluation.” Its goal is to test the strength of the IS (Information Systems).
The significance of pentesting
As computer attacks become more complex, the need for intrusion tests grows. For companies to effectively halt attacks, they must enhance their capabilities. This requires constant monitoring, as well as very frequent pentests. These are crucial for identifying security vulnerabilities, addressing them, and thereby boosting the protection of the information system.
Although hiring a pentester represents a substantial investment, companies are strongly encouraged to utilize this cyber expert. In the event of cyber attacks, they face the possibility of losing millions, or even billions, of euros due to operational disruptions, demands for ransom, and damage to their reputation. This also accounts for the high demand for cybersecurity professionals across all industries.
Beyond bolstering computer security, pentesting is also essential for meeting regulatory requirements. This includes the GDPR, which mandates that companies ensure the security of their information systems to prevent data breaches. For organizations seeking certification (such meant as ISO 27001), penetration testing is a necessary precondition for approval.

Vulnerability scanning and Pentest
In the realm of cybersecurity, companies can execute a series of tests to fortify the security of their IS. Among the most frequent are vulnerability scans. Their purpose is to uncover weaknesses in the computer system. This is somewhat akin to a pentest.
In fact, not quite the same. For starters, because vulnerability scanners are automated tools that search for the most common vulnerabilities in a network or an application. Unlike these, a pentest involves an in-depth and manual examination of each vulnerability. This enables the identification of weaknesses that automated tools cannot detect.
Moreover, vulnerability scanners only spot the flaws. They don’t fully exploit them to grasp all the potential consequences. On the contrary, a pentest simulates an actual cyber attack. It is capable of recognizing all types of vulnerabilities, as well as their impacts and possible ramifications.
Nevertheless, this doesn’t suggest that vulnerability scans should be disregarded. They represent a less expensive and more straightforward preliminary step that allows companies to maintain a basic level of security.
What are the different types of penetration tests?
Given the complexity of information systems, pentests can target various components. Hence, they are categorized into several types. Below are the most common ones:
- Internal network penetration test: it zeroes in on servers, network equipment, workstations, WI-FI, Active Directory, etc. Its aim is to evaluate the security of the internal network from the perspective of an attacker who has already gained access.
- Web application penetration test: it involves searching for vulnerabilities stemming from the configuration of the infrastructures that host the services (servers, cloud environments).
- Mobile application penetration test: this type of test includes both a static and a dynamic analysis of the application. Static analysis aids in extracting elements for attempting reverse engineering, while dynamic analysis involves hunting for vulnerabilities within the application during runtime.
- API penetration test: this can be conducted either as a standalone or as part of a web or mobile application penetration test. APIs have specific vulnerabilities, such as broken authentication, unbounded resource consumption, server-side request forgery, etc.
- IoT systems and connected devices penetration tests: every layer of the IoT ecosystem is analyzed, including hardware, firmware, communication protocols, servers, web applications, and mobile applications.

What is the methodology for conducting a Pentest?
3 pentesting methodologies
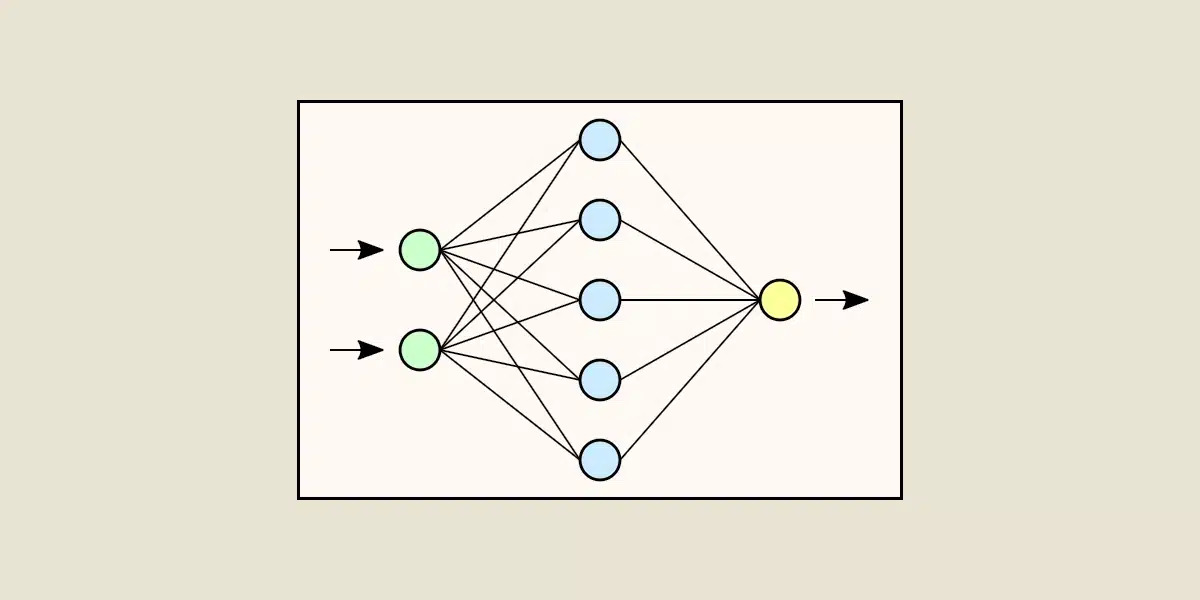
Prior to delving into the steps of pentesting, it’s important to note that penetration tests can be undertaken using three different approaches:
- Blackbox pentest: the pentester doesn’t have access to the information system’s data. They approach the system as an outsider to the organization.
- Greybox pentest: the pentester has access to some information but not all. For instance, certain user accounts.
- Whitebox pentest: the pentester has full access to all the available data, including the source code and the system administrator account of the information systems.
By employing these different methodologies, one can prepare for all kinds of attacks.
The 8 steps of penetration testing
To conduct a pentest, the cyber expert must adhere to a detailed plan consisting of 8 steps:
- Target reconnaissance: this step involves gathering data about the nature of the test (network, API, application, …) and the specified target.
- Mapping: this is the process of creating a map of the information system. Its purpose is to list assets.
- Vulnerability research: this is when the pentester examines the IS for weaknesses.
- Exploitation: the pentester utilizes the identified vulnerabilities to assess their severity.
- Privilege escalation: the pentester assumes the role of a hacker, temporarily acquiring administrator rights (the privileges) to execute their attacks.
- Propagation: this involves determining the extent of the vulnerability. To do this, the pentester expands their attack to other devices within the IT infrastructure.
- Cleaning: the system is cleansed and reverted to its original state.
- Reporting: the pentester documents all the actions performed during the penetration test and offers recommendations for remedying the deficiencies.
Throughout these stages, the pentester utilizes a variety of tools, such as Burp Suite, Kali Linux, Metasploit, Hashcat, Nmap, Ettercap, SQLmap, etc.
Train in pentesting with DataScientest
As the demand for pentesters rises among companies, there’s currently a shortage of skilled professionals. If you aim to assist organizations in fortifying their computer systems, becoming a cyber expert is your calling. But first, you’ll need proper training. Thanks to DataScientest, you will be equipped to conduct all kinds of tests to thwart pirate attacks.