During the development of a software programme or application, dozens or even hundreds of users are involved. But not all of them have the same access rights. So if you want to customise access to the various resources on the Google Cloud Platform, there's GCP Custom.
What is GCP custom role?
GCP custom roles correspond to custom roles on IAM (Identity and Access Management).
GCP custom role on IAM
As a reminder, IAM is the authentication and access management platform on the Google Cloud Platform. More specifically, it defines who (user) has access to what (resources) and how (role).
- The user: also known as the main account. This can be a Google Account, a Service Account, a Google Group, a Google Workspace account or a Cloud Identity domain. Each main account has its own identifier (often an email address).
- Cloud resources: these are Compute Engine virtual machine instances, Google Kubernetes Engine clusters, Cloud Storage buckets, complete folders, projects, etc.
- The role: access authorisation is not granted directly to the user, but goes through the intermediary of roles. Roles are assigned to the main accounts and group together a set of authorisations for a resource. However, there are different types of role.
The different types of role
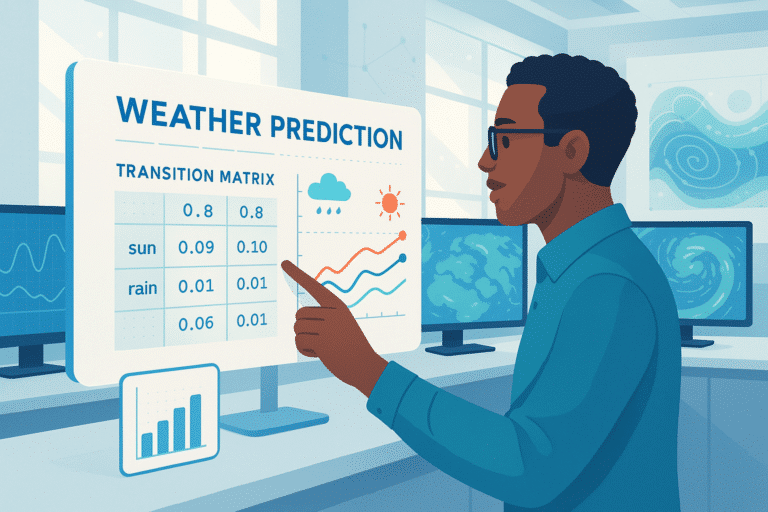
Cloud IAM has 3 types of roles:
- Basic roles: these are present in IAM by default. These are the “Owner”, “Editor” and “Reader” roles. Once assigned, these roles include thousands of authorisations on GCP resources. It is therefore preferable not to assign this type of role.
- Predefined roles: entirely managed by Google, these allow you to authorise or deny access to resources. When new features or services are added, the predefined roles are automatically updated.
- Custom roles: these are defined by the user themselves. This makes it possible to adapt accessibility conditions to the specific needs of the organisation. But with these custom roles, there is no automatic update when a new feature or service is added.
- GCP custom roles are based on the principle of least privilege. This means that users should not have more authorisations than necessary. So when a predefined role includes authorisation for a set of resources, the creation of a GCP custom role makes it possible to give access rights for a very specific resource rather than for the whole.
Good to know: very often, it is the system administrators themselves who define the personalised roles according to the needs of the users. But in some cases, they can also use role recommendations (particularly if the assignments are too permissive). In this case, they will receive a recommendation to create a custom role.
How can I customise the roles on GCP?
Find out more about the different stages involved in creating a custom GCP role.
Obtaining authorisations
First of all, you need to obtain the authorisations to manage the roles. This means modifying, listing, deleting or creating roles. To do this, you need to obtain the role of “roles administrator” (for a project) or “organisation roles administrator” (company-wide).
View available authorisations
The management of GCP custom roles depends on their location. For example, if the role is located at organisation level, it will not be possible to include a permission in a custom role at project level.
This is why it is essential to check the list of available permissions before creating any custom roles. To list them, you can use the Google Cloud Console or the Identity and Access Management API.
Obtaining metadata
Before you can create a GCP custom role, you need to know its metadata. In other words, the role ID and all the authorisations it contains. Here again, the Google Cloud Console and the IAM API allow you to display this metadata.
Create a custom GCP role
Roles are created either at organisation level or at project level (never at folder level). For the latter, it is preferable to define a role at organisation level, since they can include all the authorisations compatible with GCP custom roles. But some can only be used at the level of the organisation, not the project. This is the case, for example, with resourcemanager.organizations.get.
Next, to create a custom role, you need to comply with the following rules:
- 3,000 authorisations maximum ;
- 64 KB maximum for the size of the title, the description and the authorisation names.
If you need to assign more authorisations, you can distribute them between several custom roles on GCP.
To create a custom role on Identity and Access Management, you can use the Google Cloud Platform console, the IAM API or the various programming languages (C++, C, Go, Java, Python).
Include a launch stage
This launch phase is optional. The idea is to test the custom role before deploying it on a large scale. This is particularly important for the DISABLED function, which involves deactivating the GCP custom role.
Modifying a custom role
Once a GCP custom role has been created, the easiest way is to use the read-modify-write model. This allows you to update the metadata of a resource (in particular the roles). However, when you make changes, make sure that you are the only one doing so.
If two owners are using the read-modify-write model simultaneously, errors can occur (failed modifications).
To avoid these conflicts, don’t hesitate to use the etag property, which compares the values in the request with the existing etag value.
Good to know: some updates do not appear automatically, but after a delay of up to 24 hours. This is the case, for example, with the addition or removal of the following authorisations: resourcemanager.organisations.get, resourcemanager.folders.get or resourcemanager.projects.get.
Master custom role GCPs with DataScientest
Very often, the use of GCP custom roles is the prerogative of the administrator. To master this functionality on the Google Cloud Platform, you can take GCP certifications. But to develop your full knowledge of this cloud service, it’s best to take a full training course. That’s exactly what DataScientest offers. Come and join us!